This week, we have seen vulnerabilities in 3 million car alarms, snowboard helmets, and virtual worlds. In other news, there is a new API security platform built around OpenAPI contracts. We also take a look at the SANS checklists and HTTPS/TLS tutorials.
Vulnerabilities
This was a good week for PenTestPartners. They have uncovered a couple of serious API vulnerabilities:
The first one is in Pandora and Viper (Clifford) car alarm systems. These systems control about 3 million vehicles. The vulnerability in question is an Insecure Direct Object Reference (IDOR) attack, in which attackers use security token of one user to access data of someone else. What made it worse was that the user IDs could be just enumerated. Attackers created demo accounts for themselves to access the APIs. After that, they could simply go through the IDs, get information about the users, reset their passwords, and take over the accounts. Full access provided them all information about the vehicles, and even allowed the attackers to send commands to them, such as killing the engine.
The other vulnerable API was found in Outdoor Tech CHIPS smart headphones for skiing and snowboarding. These helmet headphones can play music and allow skiers and snowboarders to talk to their friends à la walkie-talkie. The walkie-talkie functionality is cloud-based and goes through the company servers. The APIs for that functionality are highly insecure. They allow account enumeration, and for every account, they leak name, email, GPS, and audio stream.
Elsewhere, virtual worlds can be as vulnerable. A research team (Ibrahim Baggili, Peter Casey, and Martin Vondráček) at the University of New Haven found multiple vulnerabilities in the popular Bigscreen virtual reality app and its underlying Unity APIs. Inputs were not sanitized, so attackers could inject JavaScript and take control. They could discover private rooms, secretly eavesdrop discussions, see user screens, get access to their microphones, and so on.
Tools
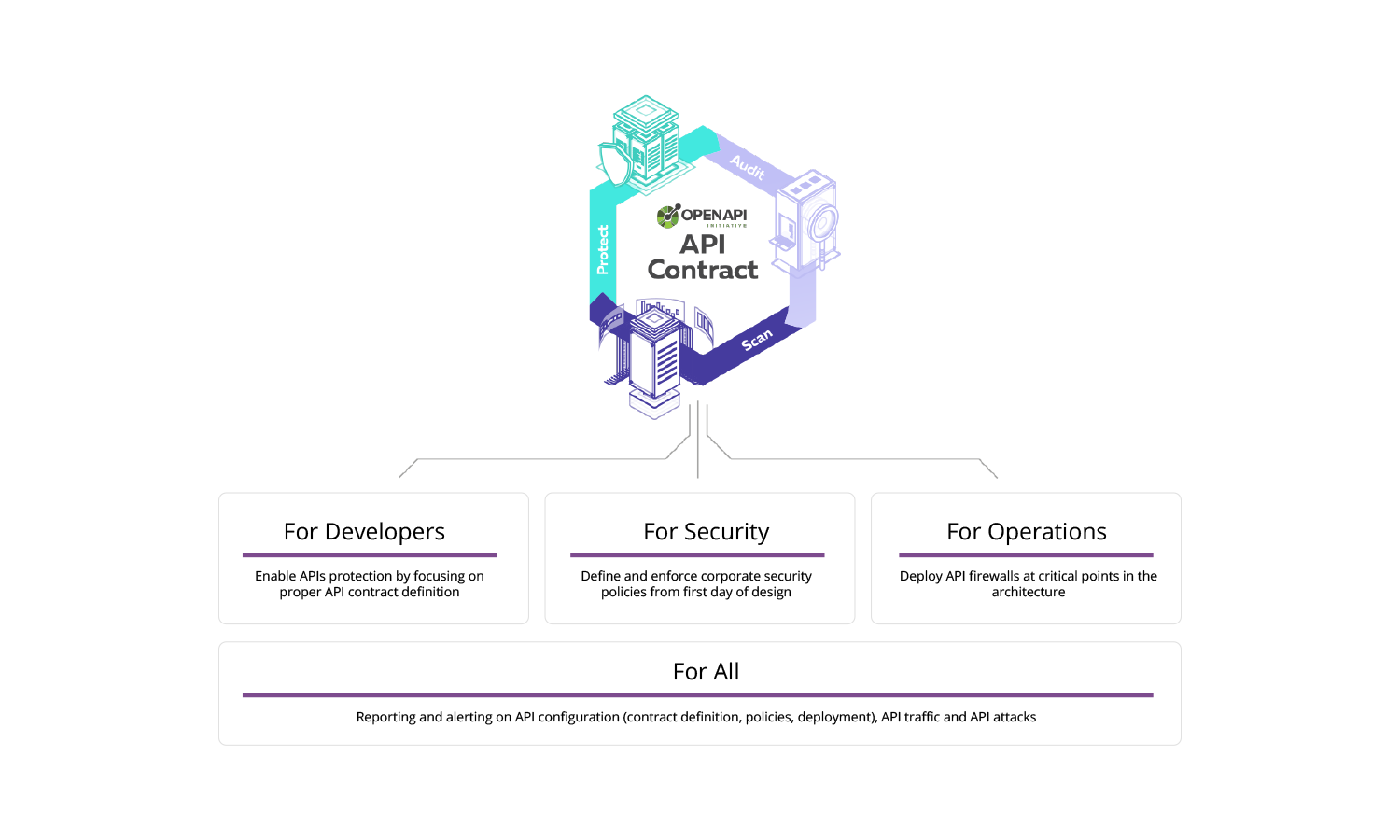
42Crunch Platform, a cloud-based API security platform is out. It provides DevSecOps process built around the OpenAPI definition of your API:
- Audit the API contract for vulnerabilities. This is similar to the Security Audit tool at APIsecurity.io.
- Scan the live API endpoint for contract compliance to ensure that the API implementation matches the API contract.
- Protect the API with a micro API firewall (including Kubernetes sidecar model) that uses a positive security model based on the API definition. This ensures that only calls and responses that match the API contract go through.
(Disclosure: I work at 42Crunch.)
Tutorials
Want a better understanding of how encryption behind TLS and HTTPS works? Check out these Computerphile videos:
These tutorials are very easy to grasp, entertaining, and educational.
Best Practices
SANS Institute published their Securing Web Application Technologies (SWAT) Checklist. It covers in detail:
- Error Handling and Logging
- Data Protection
- Configuration and Operations
- Authentication
- Session Management
- Input and Output Handling
- Access Control
Subscribe to this weekly newsletter at https://APIsecurity.io
Get API Security news directly in your Inbox.
By clicking Subscribe you agree to our Data Policy