This week, we had another mobile app leaking user data, and the first ever CEO resignation because of an API breach. There’s also:
- The best practices for AWS API Gateway security
- Gartner’s advice to CISOs on cloud security
- Security implications of the OpenAPI Specification (OAS)
- Vulnerabilities in machine learning
Vulnerabilities
The mobile application 63red Safe had an API breach. This app is a Yelp-like app for US conservatives. A security researcher found the credentials of the app’s author included in the app’s source code. The code also had a list of API endpoints for storing or retrieving data. The backend APIs in question didn’t use any form of authentication. Anyone could look at the app’s source code, get the credentials, get the API endpoints, and extract data from the app’s server with no challenge or restriction.
Lessons Learnt
New details emerge from the LandMark White breach that we covered in issue 21 in early March.
LandMark White used to be Australia’s largest independent property valuation and consultancy firm, and their APIs were used by all major banks in Australia. Now, the company is in crisis. Major customers have left and several executives have had to step down.
It turns out that some teams at Landmark White actually knew about the API vulnerability before the breach happened, and for about 18 months at that! The information just never reached the right people. Talk about the importance of a shared view on the state of API security in your company.
Best Practices
Daria Kirilenko from Gartner provides the following advice to chief information security officers (CISOs) on cloud security:
- Understand that cloud security is shared between vendors and your internal team.
- Build a cloud security team.
- Build an internal common security platform for APIs and different reference architectures.
Ory Segal, CTO of PureSec, shares his security best practices for AWS API Gateway:
- Use different types of APIs for different types of access:
- Public
- Authenticated
- Internal
- Use the access control mechanisms on offer to control the access to your APIs:
- API keys
- AWS IAM roles and policies
- Amazon Cognito
- AWS Lambda authorizer functions
Technology Overview
JAXenter is running my story on why API security is hard, what makes OpenAPI Specification so attractive, and how the free API Contract Security Audit tool comes in handy.
Research
Nicholas Carlini from Google demonstrated hacking machine learning (ML) by tweaking the input signal. For example, he caused the algorithm to report guacamole when actually shown a cat image, and ‘think’ it was hearing a Charles Dickens text narration when in reality (tweaked) Bach music was playing.
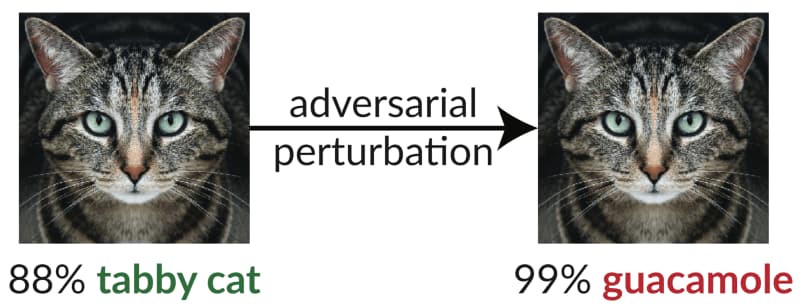
This is fascinating because so many security solutions these day rely almost 100% on ML or AI. See the summary from his RSAC session or check out the full paper.
Get API Security news directly in your Inbox.
By clicking Subscribe you agree to our Data Policy